USB Benefits: Isolate, Convert, Extend & Connect
10/22/2018
USB was a great leap forward. Its convenience, flexibility, and interoperability have simplified everything from cabling to device installation. You can connect up to 127 devices using a single port. You can connect new peripherals without opening your computer to insert an expansion card. Devices are
But as good as it is, USB was designed with safe office and IT environments in mind. When it moves out into the real world, as it is currently doing in industries ranging from manufacturing to
USB’s Range Limitation: Conversion and Extension
In a straight line, USB’s
You can address the USB range limitation through extension and conversion. For example, in situations where installing a local PC would be impractical, as
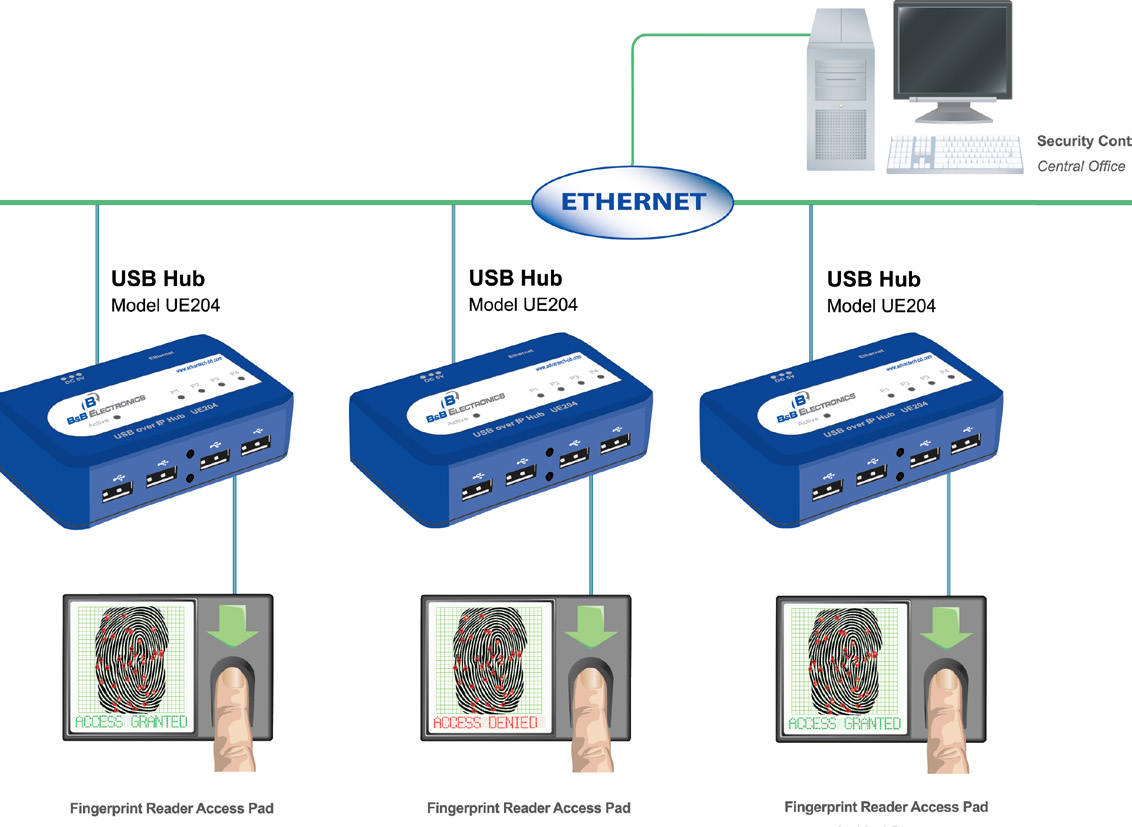
Figure 1. USB to TCP/IP Ethernet Communication
In some
Figure 2. Ethernet Extenders-Copper, DSL, Fiber Communication
And, although serial communications protocols pre-date USB by decades, there is no need to leave your legacy serial devices out of the loop. You can acquire USB-to-serial converters for virtually any application, from heavy-duty, multi-port, DINrail mounted converters to simple inline converters that USB enable just a single device. (See Figure 3.)
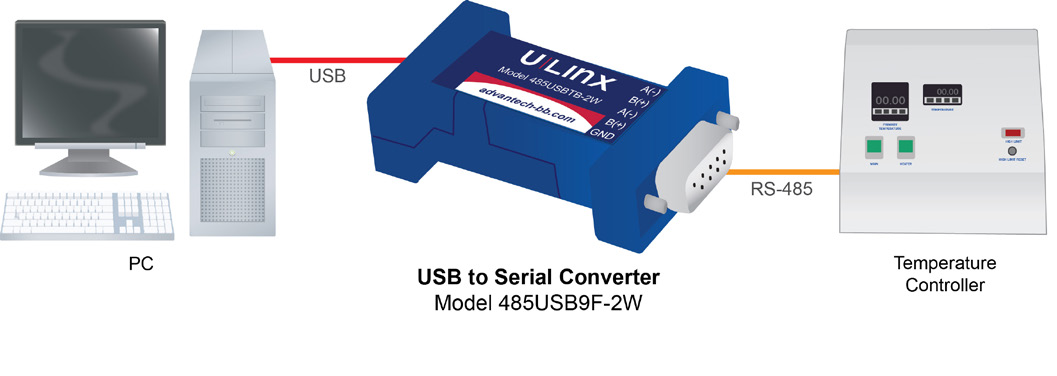
Figure 3. USB to Serial Application
Spikes, Surges and Ground Loops: The Need for Isolation
USB cables behave well enough in the home office, but in industrial
USB cable contains four wires: two are for data and two carry 5 VDC power for downstream devices. Isolation works by changing the nature of the signal on the two USB data lines and transforming the 5 VDC power on the other pair. The isolator protects the data lines by converting the signal to either

Figure 4. USB isolators protect data lines against power surges,
Note that isolators will limit the USB data rate to “Full Speed”, or 12 Mbps. This happens because USB devices default to Full Speed until they are able to negotiate a higher connection rate with the USB hub. The negotiation is initiated by the device, which drives 17.78mA into the D- data line for at least a millisecond, creating what is called a K-chirp.
If the hub is “High Speed” (480 Mbps) capable, it will respond by alternately injecting 17.78 mA into the D- and the D+ lines. When the device has detected at least 3 of these chirp pairs it will decide that the hub is High Speed capable, and it will establish the connection at the higher data rate.
Unfortunately, isolators interfere with this negotiation when they convert the DC signal to AC
The Right Way to Connect
Older cables were connected with exposed pins that could be bent or broken. USB cables protect their pins inside the connector housing. You may connect and disconnect them over and over again without doing any harm. The design has proven to be quite reliable in desktop applications.
But industrial environments are less benign. Vibration can cause USB cables to work themselves loose and minor tugging will do the same thing. When that happens in a home office a typical result might be that the printer seems to have stopped working. It is an easy fix.
But, in industrial applications, it can mean serious data loss and downtime. And, if flammable substances are present, USB’s 5 VDC power is enough to pose a risk for fire and explosion. It would be impractical to abandon USB, so some manufacturers are addressing the problem by developing high retention USB ports. They closely resemble the ports you see in office-grade equipment and plugging in a USB cable feels almost as effortless, but the difference in industrial safety is enormous. A typical high retention port can grip a cable firmly enough to resist 3.4 lbs of force. (See Figure 5.)

Figure 5. High-retention USB ports grip standard USB cables tight.
USB may have been designed for the office environment, but it does not have to stay there. Just isolate, convert, extend and connect. If you do it correctly, you can take USB all the way out to the industrial network edge.
